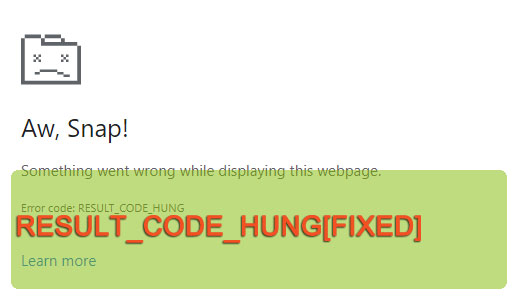
How to Fix RESULT_CODE_HUNG Errors
RESULT_CODE_HUNG is a browser based error notification that can and typically does appear in the most random circumstances. Your typical symptom is an inability to access whatever site you were on or trying to load. Other circumstances in which this error may occur includes, when accessing specific services online.