| Attention Before you read this post, I highly recommend you check out my resources page for access to the tools and services I use to not only maintain my system but also fix all my computer errors, by clicking here! |
In this post I will be discussing how to prevent phishing in all its miss-glory.
There are currently hundreds of millions of people that log onto the internet each day. These individuals may access the internet purely for research purpose, or possibly for paying their bills, the reasons why people get online are almost limitless. However, despite this reality, most of these users are completely oblivious to the potential risks once online. Phishing is basically when an individual attempts to acquire information from people online for the purpose of criminal activity; typically, this information will be used for identity fraud. The two most common phishing scams are phone scams and website cloning.
These cloned sites for example, tend to be very well made and thus, fool a great many people, so in essence, you have a situation where users are willingly giving up their own personal details. A common method in which these malicious individuals get people onto their sites is by sending unsolicited emails pretending to be a credit card or bank company, in the email, they will insist that there was an error on your account and that you will need to log back into your account to verify your details, or they may say that your account has been inactive for a considerable length of time and thus, you will need to log back into it to prevent it from being deactivated. Within this email will be a link to the company’s website, it’s this link that will take you through to the cloned website, where you will be fooled into believing you’re on an official, such scams today is what makes it increasingly important people learn how to prevent phishing scams.
These cloned sites are typically very well made, and so, can be very difficult, even for an experienced internet surfer to spot, which is why it’s so important you learn exactly how to prevent phishing scams. Anyway, once you put your account number and password into the website, your details will be retained, which can then be later accessed by the identity thieve(s).
The reality is that no company would ever send you an email notifying you of such things.
How to Prevent Phishing Scams
As each day passes more and more phishing scams enter the fray, so it’s very important you’re cognizant of these developments. While for the most part eCommerce and banking online are safe, you should always be extremely cautious whenever you’re involved in any activity that entails giving out your financial information. Below is a list of do’s and don’ts for those who would like to know how to prevent phishing.
1. The first thing you’ll want to do is scan your system on a regular basis. Make sure you have a malware, antivirus and firewall program running on your computer at all times. You should also consider scheduling the antivirus/malware programs to run automatically, at least once per week. For more information on virus/malware removal tool(s), I suggest you check out my post on the best antivirus programs.
2. If you use your own email client software like Outlook Express, Outlook 2010, IncrediMail etc, then you’ll want to prevent these malicious emails from getting into your inbox, which can be accomplished by using a phishing filter. There are a ton of different filters out there, but the ones made using Bayesian Filter architecture, such as SpamBayes tend to work the best. You can download this filter from here: http://spambayes.sourceforge.net/
A phishing filter of this quality should be able to filter out at least 90% of these emails, thus heightening your level of online security.
3. Do not open unsolicited emails. There are many phishing emails that present to you an appealing proposition or deal in hopes of acquiring your personal details. One thing you should keep in mind is that large organisations such as your bank or building society would never request your personal details through email.
4. Do not click on unverified links. If you receive an email from a bank or building society that contains a link, one way of verifying the link is by writing the link down using a pen and pad and manually typing the link into the address bar. This is an effective method of prohibiting identify thieves from hiding a redirect in a link.
5. Avoid and if possible, completely refrain from downloading executable attachments in your emails. This is because hackers like to hide malicious code inside these little .exe, .com and .scr programs. Only download files you were expecting to arrive in your inbox, i.e. an email attachment sent by a friend or family member.
6. Do not respond to emails that were not directly sent to you. If you were sent a chain email, which is basically an email that was sent out to a large number of recipients, then you should delete it as soon as possible. Phishing emails are typically sent out as chain emails, so if you’re sent one of these types of emails, there’s a good chance that it was sent with malicious intent.
7. Don’t call any unverified phone numbers. If you receive an enticing offer or service in an email that requests you call a specific phone number in order receive whatever is being offered, consider typing the number into Google search first, just as a means of verifying the legitimacy of the number.
8. All suspicious activity must be reported. If you’ve subscribed to the mailing list or service of a specific website or organisation that is being spoofed, then it’ll be a good idea for you to contact the organisation or website and report the incidences to them. This way, they should be able to pool their resources together to combat such incidences.
9. Make sure the phishing filter is enabled on your browser. If you use Internet Explorer 8 or above, then it should come with a built-in phishing filter; your browser already knows how to prevent phishing scams, as the purpose of this filter is to examine the websites that you visit and to notify you of any that are suspicious. To turn this feature on, simply do the following.
Enable Internet Explorer Phishing Filter
a. First, open up your Internet Explorer browser window.

b. Once the browser window has loaded up, click on Safety -> SmartScreen Filter -> Turn On SmartScreen Filter.
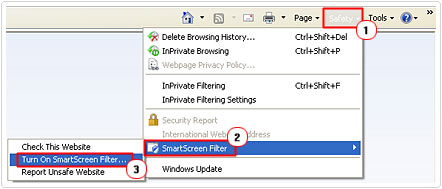
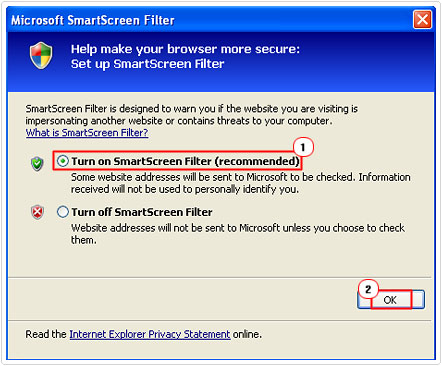
c. A Microsoft SmartScreen Filter dialog box should pop up, from here you’ll want to click on Turn on SmartScreen Filter (recommended), and then click on OK.
If you use Firefox 2 or above, then it also comes with a built-in phishing filter which functions exactly like the SmartScreen Filter on Internet Explorer; Firefox also knows how to prevent phishing scams, with this powerful tool. Anyway, to turn this filter on, simply do the following.
Enable Firefox Phishing Filter
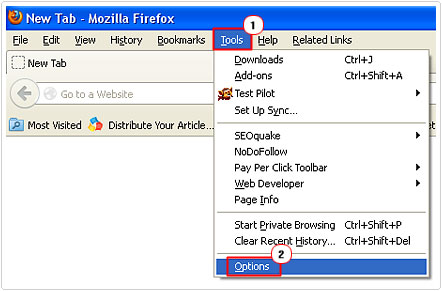
a. First, open up your Firefox browser window.

b. Once your browser is up and running click on Tools -> Options.
c. An Options dialog box will pop up, from here, click on the Security Tab, then check the boxes next to Block reported attack sites and Block reported web forgeries. Then click on OK.
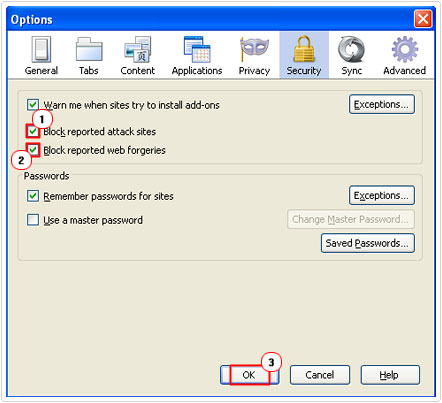
Note: to verify that the phishing filter is working, I recommend you visit the following website and click on test site: http://www.mozilla.org/en-US/firefox/phishing-protection/firefox2/
Report Phishing Scams
With the number of phishing cases on the rise, it’s in all of our best interests to do our utmost to protect ourselves by knowing how to prevent phishing scams. From the information above, you should have enough information to properly identify a phishing scam. However, there is something else that you can do to sufficiently combat these scams, and that is to report them.
Here are 2 of the most effective ways of doing that:
- Reporting the phishing scam to the APWG (Anti-Phishing Working Group) is the first thing you can do. This organisation is voluntarily run and is dedicated to curtailing the identity theft and fraud that results from these phishing emails. The APWG currently has a large archive of all the various phishing scam emails sent out to date, which has gone a long way in helping others effectively on how to prevent phishing scams. If someone sends you a phishing email, then you should copy its contents and paste it into a new email and send it to reportphishing[at]antiphishing.org. It’s very important that you make a copy of the email instead of forwarding it, as forwarding an email can sometimes result in loss of email data. You want the organisation to receive the email in its entirety so that they can suitably add it to their already growing archive.
- Another method that you can use is to report the phishing emails/scams directly to the company that is being spoofed. I spoke a little about this earlier, so now I’m going to delve a little deeper into the topic. Consider calling or emailing the company in question. If you receive a spoof email of PayPal or eBay, then you should copy its contents to a separate email (as stated above) and send it to spoof@ebay or spoof@paypal. From the information you send to them, they should be able to have the site taken down, and it will also enable the company to warn their other users about the specific website in question.
It takes no more than a few minutes, but the end result is you helping other internet users become more aware of all the scams online. When it comes to knowing how to prevent phishing sites, reporting them (as the most effective) not only protects you, but also makes the internet a safer place for all of us.
Are you looking for a way to repair all the errors on your computer?

If the answer is Yes, then I highly recommend you check out Advanced System Repair Pro.
Which is the leading registry cleaner program online that is able to cure your system from a number of different ailments such as Windows Installer Errors, Runtime Errors, Malicious Software, Spyware, System Freezing, Active Malware, Blue Screen of Death Errors, Rundll Errors, Slow Erratic Computer Performance, ActiveX Errors and much more. Click here to check it out NOW!


Thanks for posting this information. Phone scams have become prevalent indeed. As a matter of fact, the number of consumer complaints against fraudulent calls seem to be exponentially increasing.
But thanks to updates like what you have here, more people are made aware of how scams are perpetrated and how to avoid them. Although the number of complaints are rising, they’re mostly about how persistent the scammers are.